API Endpoints Getting Hammered? How High‑Defense CDN Secures Your API
Why are API endpoints becoming so easy to abuse? Many sites and apps aren’t taken down by massive traffic floods – they’re slowly killed by high‑frequency API requests. This article explains the technical side of API attacks, how a high‑defense CDN uses behavioral analysis, rate limiting, and dynamic policies to protect your APIs, and why traditional WAF and basic CDN solutions struggle against mo

Most people don’t start taking API security seriously because they read a security report.
It usually hits them one day when they notice:
- Login endpoints start slowing down
- SMS APIs get drained like crazy
- Payment endpoints time out occasionally
- Backend CPU pegs at 100%
- Database connections blow up
At first you think it’s a bug in your code.
But after hours of debugging, you realize: your API is being abused.
And there’s a clear trend: compared to traditional DDoS, more attackers are going straight for API endpoints.
Because they’ve figured out: hammering an API cripples your business faster than hitting your homepage.
We’re not doing a “what is” intro here. Let’s talk real tech: why APIs are becoming easy targets, why old‑school defenses fail, and how a high‑defense CDN actually keeps your APIs safe.
1. Why Are APIs Becoming Such Juicy Targets?
Here’s the reality: most of your site’s core logic isn’t on the page anymore – it’s in the API.
Think: login, signup, payment, checkout, search, push notifications, app data exchange.
Essentially: the page is just a shell; the API is the real business core.
Attackers know this very well. That’s why attack patterns have shifted dramatically in the last couple of years.
Back then: hit the homepage, saturate bandwidth.
Now: hammer the login endpoint, order endpoint, captcha endpoint, user lookup endpoint.
Because those places: eat more CPU, hammer the database harder, and bring down the business faster.
One thing many people underestimate: API endpoints are almost always “dynamic compute” heavy.
Unlike static pages, they can’t be cached. So as soon as request volume goes up, backend pressure spikes instantly.
2. Most API Attacks Today Aren’t About “Massive Traffic”
When people hear “attack”, they imagine hundreds of Gbps or terabits slamming the server.
But in reality, API abuse is more often: low traffic, high frequency, persistent hammering.
For example: dozens of requests per second, distributed IPs, mimicking real user behavior.
These attacks have several distinct characteristics:
1) Traffic is modest: traditional DDoS protection might miss it entirely.
2) Requests look legitimate: attackers are actually calling your API.
Headers look normal, cookies look normal, User‑Agent looks normal.
3) Extremely resource‑intensive on the backend: especially database queries, captcha validation, token verification, search logic – these get killed easily.
3. Why Traditional WAF and Basic CDN Keep Falling Short
This is the biggest headache for many engineering teams right now.
Because API attacks have become increasingly “normal‑user‑like”.
What’s the traditional WAF logic?
- IP blacklisting
- Request rate limiting
- User‑Agent filtering
- Static rule blocking
The problem: attackers have completely bypassed this playbook.
For example: residential IP proxies, human‑solving captcha farms, browser automation, AI‑driven behavior simulation.
The result: everything looks like a “normal request”.
But in reality, your API is being pounded into the ground and your backend is being choked.
That’s why so many people encounter this: bandwidth isn’t full, yet the service is already dead.
4. What Does a High‑Defense CDN Actually Do for API Protection?
Many people still think high‑defense CDN is just: “it absorbs DDoS traffic for you”.
But the real core capability today has shifted to: API behavior recognition.
In other words, it’s not just about “traffic volume” – it’s about:
- Does the request behave like a real human?
- Is the calling pattern abnormal?
- Does the API usage make sense?
5. Truly Effective API Protection Typically Uses Multiple Layers
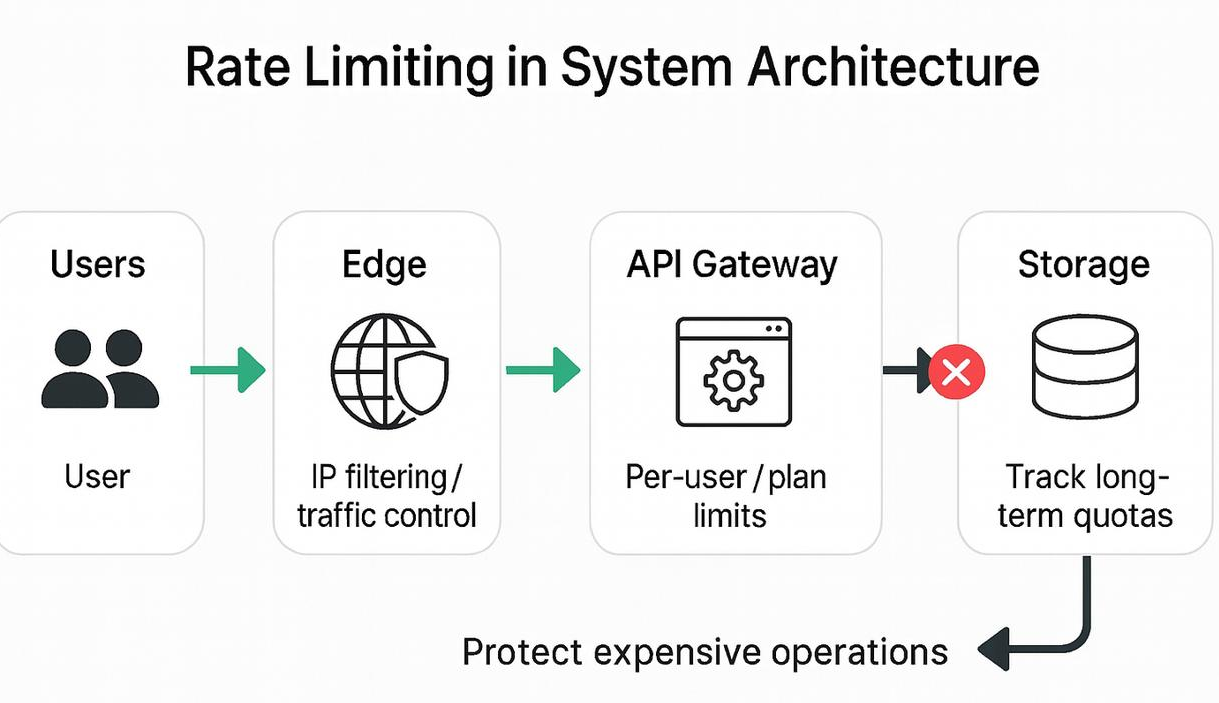
1) Edge Rate Limiting
This is the most basic layer.
For instance: requests per second per IP, access frequency for a specific endpoint, token call counts.
Exceed the threshold → blocked.
But here’s the thing: rate limit alone is no longer enough.
Because attackers will: rotate IPs, distribute requests, lower per‑source frequency.
That’s why the next layer is more critical.
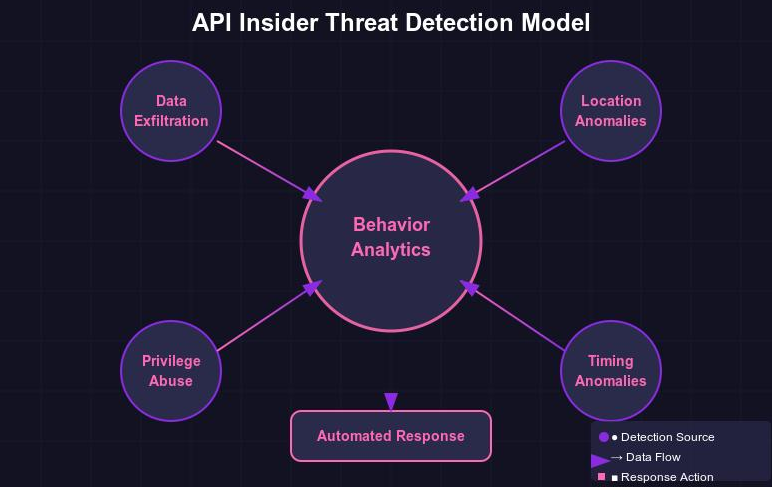
2) Behavioral Analysis
This layer starts to truly separate: real human
from script/bot
It analyzes things like:
- Request intervals
- Mouse movement patterns
- Header consistency
- TLS fingerprint
- Token behavior
Some high‑defense CDNs are already using: AI models, risk scoring, dynamic reputation systems.
To determine the intent of each request.
Solutions like CDN07 – which lean toward high‑defense – are placing more and more emphasis on “dynamic policy protection” instead of traditional static rules.
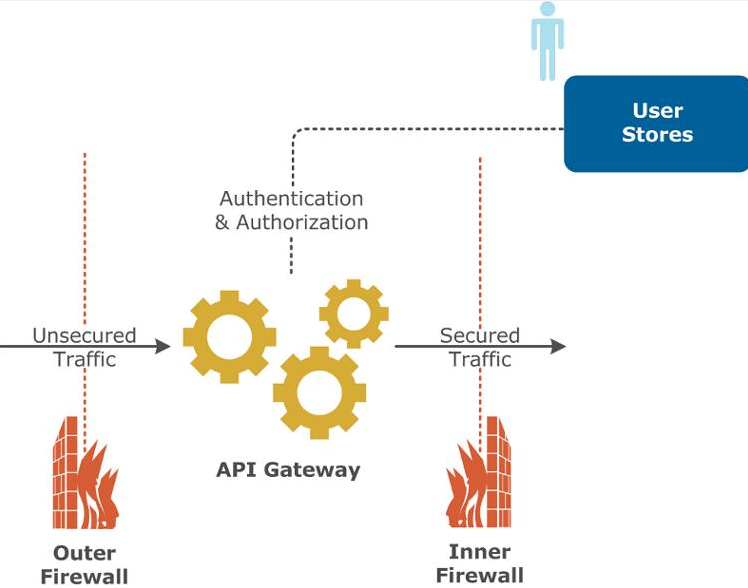
3) API‑Endpoint‑Level Protection
This is something many basic CDNs simply can’t do.
More advanced high‑defense solutions will assign independent policies to: login endpoints, payment endpoints, captcha endpoints, search endpoints.
Example: login endpoint
Focus on preventing: brute‑force, credential stuffing, token harvesting.
Search endpoint? Focus on: high‑frequency queries, crawler scanning, data scraping.
6. Why Do Many API Protection Solutions Make the API Slower?
This is a very real issue.
Many teams adopt some “security solution” and then find:
- API response times increase
- Latency goes up
- App experience degrades
The reason is simple: the protection policy is too heavy.
For example: deep inspection on every request, full captcha challenges on everything, frequent back‑origin analysis for each call.
Result: the attack isn’t dead yet, but your real users are already suffering.
That’s why truly mature high‑defense CDNs emphasize: edge identification, intelligent caching, dynamic policies, layered detection.
Not “one size fits all” for every request.
7. A Real Trend: API Protection Is Becoming the Main Battlefield
Over the next few years, this trend will become impossible to ignore: the homepage is no longer the prime target – APIs are.
Because today:
- Mobile apps run on APIs
- Mini‑programs run on APIs
- Games run on APIs
- SaaS runs on APIs
Whoever controls the API, controls the business.
So you’ll notice that serious attacks nowadays are rarely: “saturate bandwidth, crash the homepage.”
They are: directly kill the API layer.
8. One Harsh Truth at the End
Many teams still think: “Our API isn’t public, nobody will hit it.”
But the reality is: JavaScript can be reverse‑engineered, apps can be decompiled, APIs can be scanned.
An API is never “invisible”.
The real security mindset isn’t: “hope nobody finds it.”
It’s: “even if they find it, they can’t kill it.”
FAQ
1. Why are API endpoints easier to attack than web pages?
Because APIs sit closer to the business core.
Regular web pages can often be cached. But APIs typically need to: query databases in real time, generate dynamic data, perform authorization checks, execute business logic.
That means: for the same number of requests, APIs consume far more server resources than static pages.
Attackers are fully aware of this.
That’s why a huge chunk of today’s attacks go straight for: login endpoints, search endpoints, payment endpoints, token endpoints.
Because those are the easiest places to cripple the backend.
2. Why do many API attacks have modest traffic but still crash the server?
This is the biggest difference between API attacks and traditional DDoS.
Traditional DDoS: compete in bandwidth and traffic volume.
API attacks: compete in “resource consumption.”
Take a complex search endpoint: it queries the database, sorts results, evaluates permissions.
Even if the attacker sends only: tens of QPS, maybe a few hundred QPS.
It can still cause: CPU spikes, MySQL connection exhaustion, Redis blocking.
So: API attacks often don’t “kill by traffic” – they “kill by compute.”
3. Why can’t a regular CDN defend against API attacks?
Because a regular CDN was never designed for “business security.”
Ordinary CDNs excel at: static caching, image acceleration, video delivery.
But API requests are typically: uncacheable, dynamically generated, require back‑origin fetching.
That means: attack traffic still ends up hitting your origin server.
And most basic CDNs can only do: simple rate limiting, basic WAF rules.
Against modern API attacks: distributed IPs, browser automation, AI‑simulated behavior.
They’re almost blind.
4. Why is Rate Limit no longer enough to stop real attacks?
Because the attack methods have changed.
Old days: one IP hammering like crazy.
Now: tens of thousands of IPs making low‑frequency requests, each looking like a normal user.
For example: each IP makes only 1‑2 requests per second – looks completely normal in isolation.
But when aggregated: your API still gets crushed, your database still melts down.
That’s why modern high‑defense CDNs rely more on: behavioral analysis, risk scoring, TLS fingerprinting, request‑chain analytics.
Not just “rate limiting.”
5. Why are APIs especially vulnerable to CC attacks?
Because a CC attack essentially mimics real business traffic.
And APIs are naturally: lightweight, easy to automate, easy to script.
Attackers don’t even need huge traffic.
They just need to: emulate app requests, carry normal headers, include cookies and tokens.
Many systems will mistakenly think: “this is a normal user.”
Especially: login endpoints, captcha endpoints, search endpoints.
Those become prime targets.
6. How does a high‑defense CDN tell “real human” from “script”?
This is the core technology area for modern high‑defense systems.
More advanced systems will analyze a combination of factors:
Network layer: IP reputation, ASN, TLS fingerprint.
Behavior layer: click rhythm, request intervals, page flow logic.
Device layer: browser fingerprint, Canvas fingerprint, WebGL fingerprint.
Risk model: AI‑driven behavior scoring, dynamic reputation system.
The ultimate goal is one thing: determine if the request “acts like a real human.”
Solutions like CDN07 – which lean toward high‑defense – are also putting more emphasis on dynamic behavior recognition instead of traditional static rules.
7. Why do many API protection solutions make the app feel sluggish?
Because those solutions: “they achieve security, but they kill the user experience at the same time.”
For example: deep validation on every request, challenging every endpoint, back‑origin analysis for all traffic.
Result: higher API latency, slower app loading, frequent user disconnects.
The real secret to a mature high‑defense CDN is: “intelligent edge processing.”
In other words: heavy scrutiny for risky requests, fast pass‑through for normal traffic, filtering at the edge node.
Otherwise: the attack won’t kill your service – but your own protection will.
Share this post:
Related Posts
How to Speed Up Access from Mainland China to Overseas Servers? These Are the Most Effective Solutions
How can you improve access speeds from mainland China to overseas servers? In this post, we’ll break...

Which High-Defense CDN Is Most Stable for Mainland China? These 5 CDN Providers Are a Must-See!
Looking for a stable high-defense CDN for mainland China? Many global CDNs suffer from high latency,...

What Can a DDoS‑Protected CDN Actually Stop? A Complete Guide
What kinds of attacks can a CDN with DDoS mitigation actually handle? From volumetric DDoS to CC att...
