How to Choose a High-Protection CDN? These 3 Key Factors Matter Most
Choosing the wrong high-protection CDN can lead to downtime, lost traffic, and serious business disruption during an attack. In this guide, the CDN technical team breaks down the 3 most important factors that actually determine whether a high-defense CDN can handle real-world attacks: traffic scrubbing capacity, node scheduling performance, and attack detection intelligence. A practical reference
Most people only start looking for a high-protection CDN when things are already going wrong — the website is under attack, services are going offline, customers are complaining, and the team is scrambling to find a solution.
Once you start comparing providers, you quickly notice a very real problem: every company claims to offer “high protection,” every provider says they’re “stable,” and everyone advertises massive protection numbers.
But here’s the reality: those numbers alone don’t actually tell you whether the CDN can survive a real attack.
So instead of marketing hype, let’s focus on what truly matters: when choosing a high-defense CDN, there are only 3 core metrics you really need to evaluate.
1. Real Traffic Scrubbing Capacity
This is where most people get misled by flashy “protection numbers.”
You’ll often see claims like 300Gbps protection, 500Gbps protection, or even 1Tbps protection.
Sounds impressive — but in reality, many of those figures are just marketing labels, not proven attack resistance.
What actually matters isn’t the advertised number. What matters is whether the CDN can continuously absorb attacks without collapsing, whether it can withstand prolonged attack traffic, and whether it supports hybrid attack mitigation instead of only handling large-volume floods.
How do you verify this?
Ask the provider these questions directly:
- Do they support real attack simulations or stress testing?
- Do they have case studies involving sustained attacks?
- During an attack, do they throttle traffic or downgrade services?
If they can’t answer clearly, there’s a good chance the protection capability is mostly marketing.
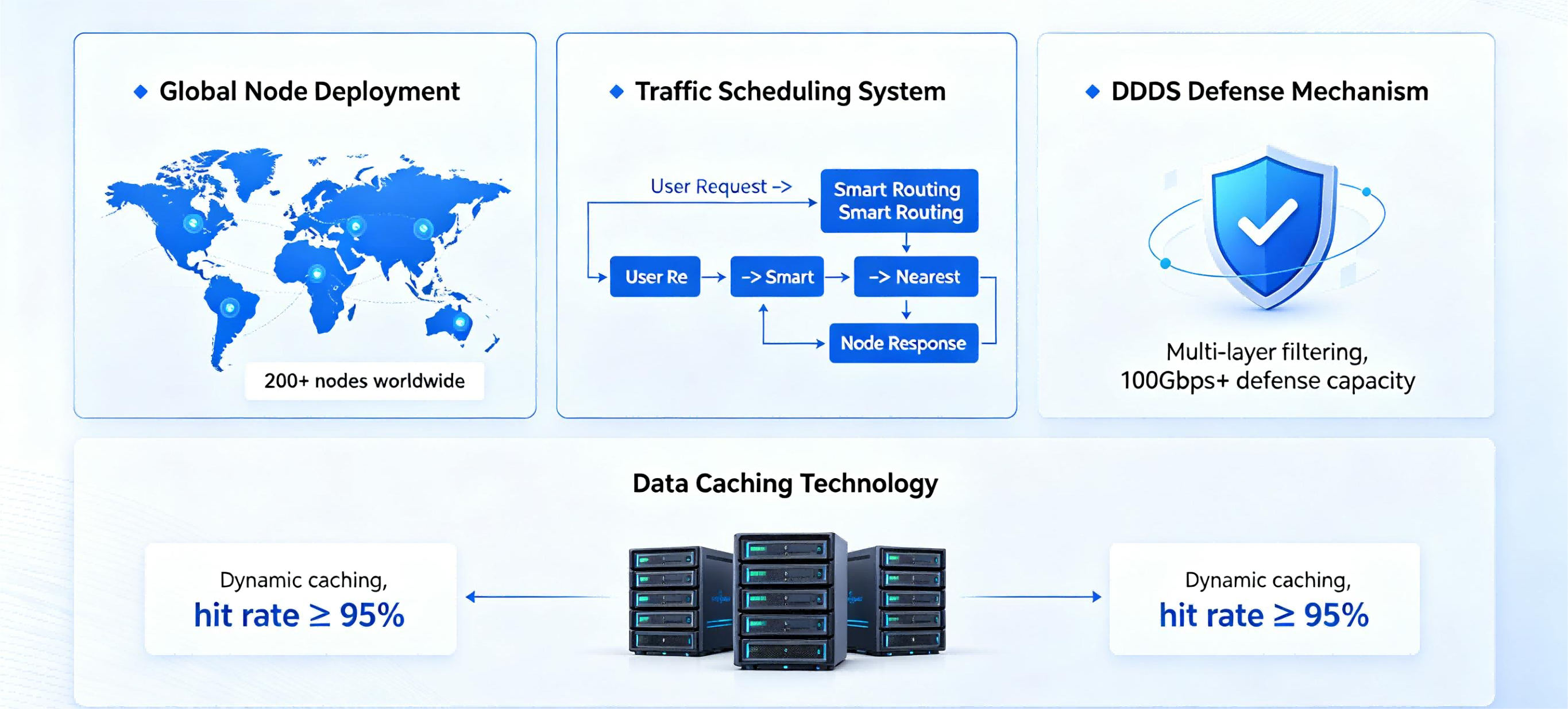
2. Global Node Infrastructure & Traffic Scheduling
One thing many businesses overlook is this: attackers usually target your CDN entry points, not your origin server directly.
If your CDN network has limited nodes, insufficient bandwidth, or poor geographic distribution,
then the result is simple: once traffic concentrates on a few nodes, those nodes get overwhelmed fast.
When nodes fail under pressure, two things happen immediately: the attack traffic falls back to your origin server, and your services become inaccessible for users.
A reliable high-protection CDN should provide: multi-region nodes (especially across Asia-Pacific and international routes), large-scale bandwidth pools, and intelligent traffic scheduling that automatically redistributes attack traffic in real time.
Solutions like CDN07 focus heavily on traffic scheduling architecture instead of acting as a simple content distribution layer.
In plain English: having more nodes isn’t enough — the network needs to stay online even under heavy attack.
3. Intelligent Attack Detection & Behavioral Analysis
Many websites don’t crash instantly during attacks — they slowly become unusable.
You’ll notice symptoms like pages loading slowly, login requests timing out, or APIs responding with extreme latency.
In most cases, this is caused by CC attacks or API abuse consuming server resources.
These attacks are especially dangerous because they often use relatively low traffic volumes and generate requests that appear legitimate, making them difficult to block with basic firewall rules.
That’s where advanced protection matters: behavioral analysis, request frequency monitoring, and intelligent path analysis.
A truly effective high-defense CDN should automatically detect abnormal traffic behavior, dynamically rate-limit suspicious requests, and block malicious activity without affecting real users.
Here’s the simplest way to think about it: bandwidth stops floods — intelligent rules stop fake users.
4. Why So Many Businesses Choose the Wrong CDN
Think about how most people evaluate high-protection CDN providers.
Usually they focus on pricing, advertised protection values, and polished landing pages.
But the real deciding factors are completely different:
Can the CDN survive real attacks? Will your services stay online during active mitigation? Can users still access your platform normally?
Those are the metrics that actually matter.
5. A Smarter Way to Evaluate High-Protection CDN Providers
If you’re comparing providers right now, follow this order:
Step 1: Verify Actual Protection Capability
- Are there real-world attack mitigation cases?
- Can they provide testing or demonstrations?
Step 2: Evaluate Network & Node Architecture
- Is the network optimized for your target audience regions?
- Does it support intelligent traffic scheduling?
Step 3: Review Security Strategy Features
- Does it include CC attack protection?
- Does it support API endpoint protection?
Only after that should you compare pricing.
Because if you prioritize cost first, you’ll usually end up regretting it later.
6. Which Type of High-Defense CDN Fits Your Business?
You don’t need to overcomplicate this. Here’s the simplest breakdown:
Small websites: entry-level DDoS protection is usually enough. Cross-border eCommerce: focus on network stability and node coverage. Gaming platforms and APIs: prioritize CC mitigation capabilities. High-concurrency platforms: enterprise-grade protection is essential.
If your business relies heavily on logins, APIs, or real-time interactions,
then attack detection and behavioral analysis become absolutely critical.
7. Final Thoughts
The best high-protection CDN isn’t the one with the best-looking specifications — it’s the one that keeps your business running when attacks actually happen.
Before making a decision, ask providers one simple question:
“If a real attack starts right now, exactly how would your system handle it?”
If the answer sounds vague, overly scripted, or avoids technical details, that’s usually a red flag.
Providers with real capabilities can clearly explain:
- How attack traffic is scrubbed
- How traffic scheduling works
- How service stability is maintained during mitigation
Share this post:
Related Posts

What Happens When Your Website’s Real IP Gets Exposed? How to Fully Hide Your Origin Server
Your website is already behind a CDN, so why is it still getting attacked or going offline? In many...
How to Speed Up Access from Mainland China to Overseas Servers? These Are the Most Effective Solutions
How can you improve access speeds from mainland China to overseas servers? In this post, we’ll break...

API Endpoints Getting Hammered? How High‑Defense CDN Secures Your API
Why are API endpoints becoming so easy to abuse? Many sites and apps aren’t taken down by massive tr...
