Why Is My Domain Resolving to 127.0.0.2? Understanding China's Anti-Fraud DNS Poisoning & How to Fix It
Is your domain suddenly pointing to 127.0.0.2? It's not a server error; it's likely China's anti-fraud DNS poisoning. This guide breaks down the engineering behind it, why it happens, and how strategic architecture and a specialized CDN can drastically reduce your risk.
Imagine this: You wake up one day and find that:
- Your domain suddenly resolves to
127.0.0.2for users in China. - It works perfectly fine everywhere else in the world, but your entire Chinese user base can't access your site.
- Your server is up, your SSL certificate is valid, and your CDN dashboard shows no errors.
Congrats, this isn't a configuration mistake on your end. You've almost certainly just run into the DNS poisoning mechanism within China's anti-fraud system.
And let's be brutally honest right off the bat: This isn't about whether your site has "illegal content" or not.
1. What Does 127.0.0.2 Actually Mean?
From an engineering standpoint, 127.0.0.2 isn't some mysterious IP. At its core, it's: A "soft-block" DNS blackhole address
It functions similarly to addresses you're probably already familiar with:
127.0.0.1(localhost)0.0.0.0(invalid address)
There's just one key difference:
Within the Chinese internet environment, 127.0.0.2 has been specifically designated as the default return value for "anti-fraud / risky domain interception."
In other words: Your site isn't "down"; the DNS resolution itself has been deliberately rewritten before your users even get a chance to connect.
2. This is (Probably) Not Your Server's Fault, or Even Your CDN's Fault
A lot of people's first reaction is:
- "Did my server get hacked?"
- "Was my DNS hijacked?"
- "Is my CDN down?"
I can tell you with a fair amount of certainty: 90% of the time, it's none of these.
Because if the problem was on your end:
- International DNS lookups would also fail.
- You'd see inconsistent IP resolutions across different regions.
- Your CDN console would likely show some kind of error.
But anti-fraud DNS poisoning has a very specific signature:
- It happens exclusively within China.
- The resolution result is incredibly consistent (127.0.0.2).
- It appears simultaneously across all major Chinese ISPs.
This tells you one thing: The interception is happening on a side you have absolutely no control over.
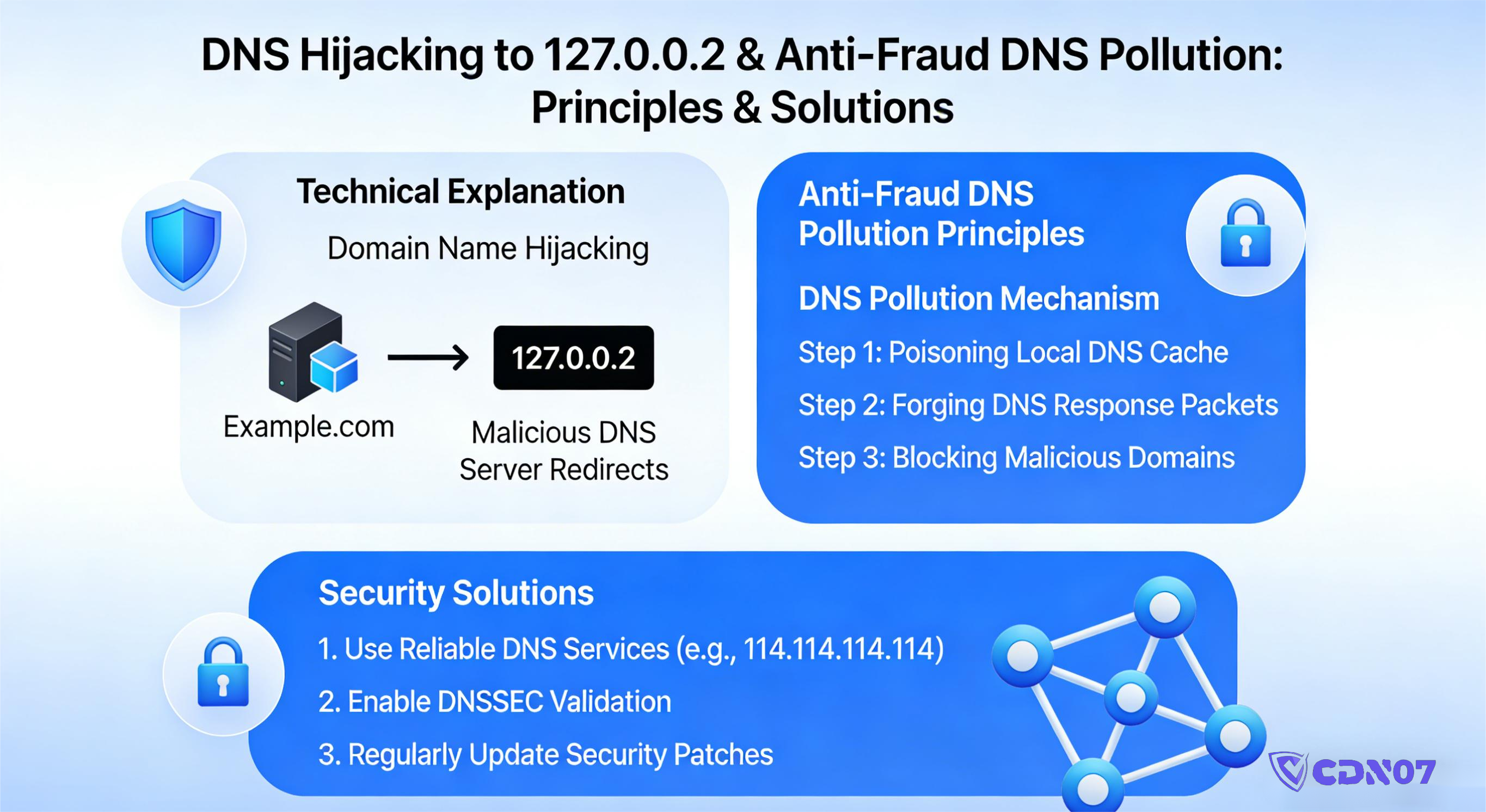
3. How Does China's Anti-Fraud DNS Poisoning Actually Work?
A lot of articles make this sound super complicated. Let's break it down in plain English.
1️⃣ The Block Isn't Happening at Your Server
The anti-fraud system isn't waiting for someone to access your site to then block the connection.
Think of it like this: It tells people the road is closed before they even start their journey.
Where exactly does this happen?
- At the ISP's recursive DNS servers
- At local gateway DNS servers
- At certain regional DNS forwarders
When a user in China runs a query:
If that domain triggers an anti-fraud rule, the DNS server doesn't return your actual A record. Instead, it returns:
And that's why the browser can't load your site.
2️⃣ Why DNS Blocking Instead of HTTP Blocking?
The reason is pretty simple: It's cheap, reliable, and minimizes collateral damage from a resource perspective.
- It doesn't matter if you're using HTTPS.
- It doesn't need to parse your content or analyze your real IP.
- It doesn't require maintaining a massive state table of blocked connections.
A DNS-level block is the simplest, most efficient way for ISPs to handle this at scale.
4. What Kind of Domains Are Most Likely to Get Sent to 127.0.0.2?
This is where a lot of site owners get genuinely frustrated.
Because I've seen countless sites that are doing absolutely nothing wrong end up in the anti-fraud blackhole.
Here's the typical high-risk profile:
1️⃣ Overseas Registration + Overseas Hosting
- Domain registered with a foreign registrar.
- DNS hosted outside of China.
- Server IP is outside of China.
To the anti-fraud system, these domains are inherently higher risk.
2️⃣ Shared IP Addresses / Pooled IPs
You might be completely legitimate, but if you're sharing an IP pool with even a few "problematic" sites, you're at risk.
Guilt by association is very common here.
3️⃣ Unusual Access Patterns in a Short Timeframe
For example:
- A sudden spike in direct traffic from China.
- High-frequency API calls.
- Behavior that looks like redirects, callbacks, or proxying.
Even if your business is totally legitimate, if your traffic patterns look like a scam operation, you can get flagged.
4️⃣ Your Domain Has a "Dirty" History
A lot of people buy expired domains without checking their history. If that domain was used years ago for something shady:
- Blackhat SEO
- Malicious redirects
- Phishing
You might be clean now, but the system doesn't automatically "forget" that history.
5. Why Does Changing Servers, IPs, or CDNs Usually Do Nothing?
This is a critical point that's almost always misunderstood.
Because: The block is on the domain name, not the IP address.
When you change your IP, all you're doing is:
You're NOT doing this:
This leads to a frustratingly common scenario:
- You switch to a new, clean IP.
- Users in China still see 127.0.0.2.
- Users everywhere else see your site just fine.
This isn't a DNS cache issue. It's a policy hit.
6. So, Is There a Solution? Yes, But It's About Risk Management, Not Guarantees
I'm not going to promise you a "100% fix." Any good engineer knows that's not how this works. But the reality is: You can dramatically reduce your chances of getting blocked, and even structure your setup to avoid it from the start.
Level 1: Immediate Mitigation (Quick Wins)
- Use a split-horizon DNS setup (separate resolution paths for domestic China and international traffic).
- Ensure traffic from China goes through a distinct resolution path.
- This reduces the likelihood of hitting the recursive DNS servers that apply the block in the first place.
Most standard CDNs cannot do this.
Level 2: Structural Anti-Pollution (The Core Strategy)
This is where the real solution lies. An effective setup will have a few key characteristics:
- Anycast with multiple entry points
- Traffic from China doesn't directly expose your real overseas origin IP.
- DNS responses are geographically aware and differentiated.
- Your domain's access path doesn't look like a scam operation.
This is exactly why specialized high-defense + anti-pollution CDN providers have a much lower rate of domains ending up at 127.0.0.2.
It's not magic. It's a fundamentally different architecture.
Level 3: "Reputation Whitening" Through Behavior
This is something you don't hear about often, but it's crucial. The anti-fraud system is behavior-driven. No one is manually monitoring your site.
This includes:
- Request frequency and patterns.
- Session完整性 (complete user sessions vs. automated pings).
- Standard TCP behavior.
- Clean redirect logic.
When your site behaves like a normal, legitimate business site instead of a "redirector," your risk profile drops significantly.
7. Why "Anti-Pollution CDNs" Aren't Just Marketing Hype
I get it. "Anti-DNS pollution" can sound like a gimmick. But here's the reality:
A competent provider with real engineering chops isn't trying to "fight" the anti-fraud system. They're focused on architecturally avoiding the false-positive models.
The core logic is simple: Make your domain look as little like a risky target as possible to the automated systems.
This includes:
- Intelligent DNS path design.
- Strategic IP exposure.
- Optimized edge node origin fetching.
- Avoiding any obvious "direct overseas connection" characteristics.
CDN07's anti-pollution solution is built precisely around this principle.
It's not about brute force; it's about navigating around the minefield.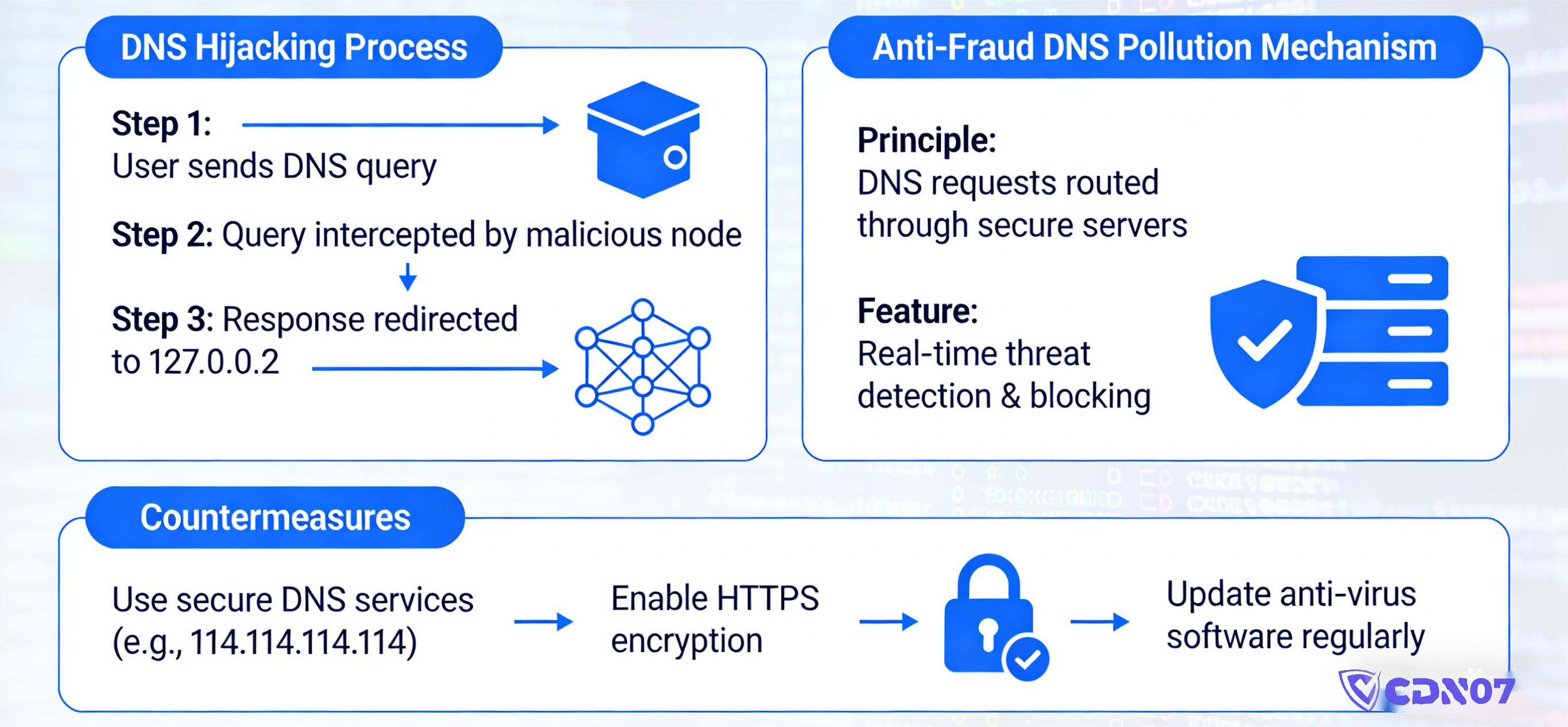
8. The Honest Truth: This Isn't a Black and White Issue
I'll end with a reality check that might not be what you want to hear, but it's the truth.
China's anti-fraud system isn't targeting your website personally. Its goal is to reduce the overall success rate of online scams.
Within that kind of massive system:
- False positives are an accepted side effect.
- Appeals processes are slow and opaque.
- Technical site owners often bear the cost of these "operational errors."
So, what can an engineer realistically do? Only one thing: Build your site to be the one that doesn't stand out.
This is exactly why:
- Architecture choices
- CDN selection
- DNS path design
Aren't just about performance anymore. Today, they're about ensuring your site remains accessible.
Frequently Asked Questions
Q1: My domain resolves to 127.0.0.2. Does that mean my site is blocked?
A: Technically, it's not a full site block. It's an interception at the DNS level. Your server is still live and accessible to the rest of the world. Users in China just get a fake address before they can even connect. A 127.0.0.2 return is serious, but it's a step away from a complete, irreversible takedown.
Q2: My site's content is 100% legal. Why would it get hit by this?
A: This is the most frustrating part. The system doesn't judge whether you are "good," it judges whether you "look bad." If your domain's characteristics, traffic patterns, or IP history share any similarities with scam operations, you can be collateral damage. Clean content does not equal a clean behavioral profile.
Q3: I changed servers, IPs, and CDNs. Why didn't it work?
A: Because the block is on your domain name, not the IP. Changing the IP is just pointing the already-flagged domain to a new server. It doesn't remove the domain from the blocklist that tells Chinese DNS servers to return 127.0.0.2. That's why people spin their wheels on this.
Q4: Does 127.0.0.2 only affect certain ISPs?
A: Not necessarily. It might start with one ISP or region, but once it's propagated to higher-level anti-fraud systems, you'll quickly see it across the board:
- China Telecom: affected
- China Unicom: affected
- China Mobile: affected
When the resolution is this consistent, you're dealing with a systemic, policy-level block.
Q5: Can I appeal this kind of DNS poisoning?
A: In theory, yes. In practice, it's extremely difficult. The process is long, not very transparent, and you often can't even figure out exactly who to appeal to. For most smaller sites, technical mitigation is a much more realistic path than administrative appeals.
Q6: What kind of site is most likely to get sent to 127.0.0.2?
A: Based on experience, high-risk sites often share these traits:
- Domain, DNS, and servers all located outside China.
- Using shared IPs or less common IP ranges.
- Traffic patterns look like redirects, API relays, or scripted access.
- The domain has a "dirty" history from a previous owner.
One factor alone isn't fatal, but combine them, and your risk skyrockets.
Q7: Is an anti-pollution CDN "fighting" the system?
A: No. A good anti-pollution CDN does one thing: lowers your probability of being falsely flagged. It uses architectural design, resolution paths, and traffic behavior to make your site look like a normal business site, not a scam operation. It's about avoiding the system's attention, not confronting it.
Q8: Can an anti-pollution CDN 100% guarantee I'll never see 127.0.0.2?
A: No one can honestly make that guarantee. But in practice, reducing your risk to well under 10% is absolutely achievable. That's why many overseas sites with a significant Chinese user base bake "pollution mitigation" into their core infrastructure from day one.
Share this post:
Related Posts

Best High-Defense SDK Game Shields: Most Stable Gaming Protection Solutions Reviewed
Dealing with constant DDoS attacks, CC floods, and player disconnects? More game studios are switchi...

How Much Should a High-Protection CDN Really Cost? Don’t Fall for Cheap Pricing Traps
How much should a high-protection CDN actually cost? Are cheap DDoS protection services really worth...

Fastest Overseas High-Protection CDN for Mainland China Access in 2026 (Real-World Performance Comparison)
Looking for the fastest overseas CDN for Mainland China traffic in 2026? This real-world comparison...
